Cyber Security Career Lifecycle®
The Information Systems Security Association takes pride in serving the information security professional for over 30 years. Providing knowledge sharing and networking opportunities for its members from around the globe and from a variety of industries. Along with reaching the monumental milestone of the 30th Anniversary in 2015, the ISSA identified the challenge of “how can we best serve our membership?”
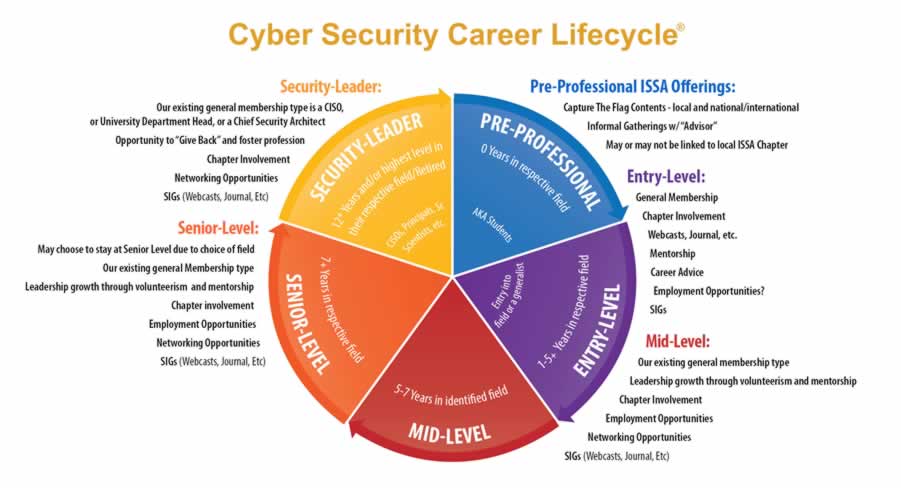
It was then, that the ISSA developed the Cyber Security Career Lifecycle® (CSCL) as a means to identify with its members. ISSA members span the information security profession; from those not yet in the profession to those who are retiring. Realizing that the needs of its members change, as individual progress through the career, so should the services that ISSA offers.
ISSA Cumulative Knowledge Model
ISSA’s approach has been that of a “Cumulative Knowledge” model, where individuals establish a foundational knowledge that is demonstrated by a degree and/or a security certification. From there, it is critical that ISSA members build on the foundation with “Just in Time” training that attempts to keep up with changes in technology and/or threats. Along with experience gained through practices and years of experience creates the Cumulative Knowledge.

Through ISSA services and offerings, our members utilize this approach for example, through networking at Chapter meetings and educational programs, through webinars offered through ISSA International and through other ISSA International training venues.
Using the Cyber Security Career Lifecycle and ISSA Services
Using the Cumulative Knowledge Module, ISSA’s members build on their knowledge and skills through services that have been designed for each phase of the CSCL.
The ISSA has identified the following benefits by investing in the CSCL model:
- An initiative undertaken by the ISSA to empower cyber security specialists to drive the destiny of the profession
- Enables professionals to define their individual career paths, provide guidance and resources to achieve their career goals
- Fulfilling our members’ needs
- Identifying and developing new and innovative services to strengthen skills sets
- Providing services based on a member’s career level
The career lifecycle has been divided into 5 stages, with the opportunity for a variety of paths within each level.
Levels and Services

Security Leader
The security leader level of the Cyber Security Career Lifecycle® is occupied by individuals who have extensive security experience, ability to direct and integrate security into an organization. These individuals have job titles such as Chief Information Security Officer, Chief Cyber Security Architect, etc. After extensive periods of leadership – some become recognized industry leaders.

Senior-Level
An individual who has extensive experience in cyber security and has been in the profession for 10+ years. These individuals have job titles such as senior cyber security risk analysis, principal application security engineer, director of cyber security, etc.

Mid-Career
An individual who has mastered general of security methodologies/principles and have determined their area of focus or specialty. Individuals in this phase of the lifecycle may have job titles such as; network security analyst, cyber security forensics analyst, application security engineer, network security engineer. Individuals who are nearing the “senior level,” may begin to hold job titles such as senior network security engineer, senior cyber security analyst for example.

Entry-Level
An individual who has yet to master general cyber security methodologies/principles. Individuals in this phase of the lifecycle may have job titles such as; associate cyber security analyst, associate network security analyst, and cyber security risk analyst for example.
Virtual Meet-Ups
So, you think you want to work in cyber security? Not sure which way to go? Not sure if you’re doing all you need to…
